How to get Sigfox Credential from CRA ?
This article describes the steps for getting credentials and flashing into modems or devices during production.
Introduction
ID, Key and PAC are credentials used in the Sigfox protocol.
This is the way to define a unique device and ensure security of data payload transmitted over the air.
Sigfox credentials can be delivered by:
- Sigfox Support with Sigfox CRA ( Central Registration Authority )
- Sigfox BUILD Platform ( limited number for product test / development phase )
- Secure Element providers. ( in this case, credentials are embedded in Secure Elements directly )
Please note that the following chapters only applies when Sigfox Credentials are delivered by Sigfox CRA (no Secure Element in the device design).
CRA Access
To get access to Sigfox CRA web site, you need to be Sigfox certified.
Any access to CRA id/key provisioning gives modem manufacturers a way get credentials for Sigfox network, in case of no Secure Element is used in its design.
Batch of credentials are requested via the Service Desk using Sigfox Verified certificate or credential number.
Some rules to respect when using CRA credentials ( ID / KEY / PAC ):
Each ID / KEY batch cannot be reused in another device.
Each ID is unique on whole Sigfox network
Each ID is independent of the subscription and token used on Sigfox network
Each ID / KEY must be flashed in the secured way in the device memory space. ( This is the manufacturer responsibility )
Only the device maker is allowed to know the KEYs for devices
Only ID / PAC must be provided to a customer to transfer ownership
PAC code is used only at first registration on backend : a new PAC code is generated by backend and must be provided to a new customer/owner if this one wants to operate this device.
CRA files must not be extracted in clear format in a factory to ensure maximum of security : decrypt on the fly and flash into device (or encrypted storage in the device)
ID / Key files are the responsibility of the manufacturer who has access to this database
CRA files and structure
You can find 2 kinds of CRA files in the CRA web site.
ID / KEY encrypted files
ID / PAC clear text ASCII files
ID / KEY encrypted file
This ID / KEY file is available on the CRA web site by any manufacturer which has certified at least one Sigfox modem.
Format
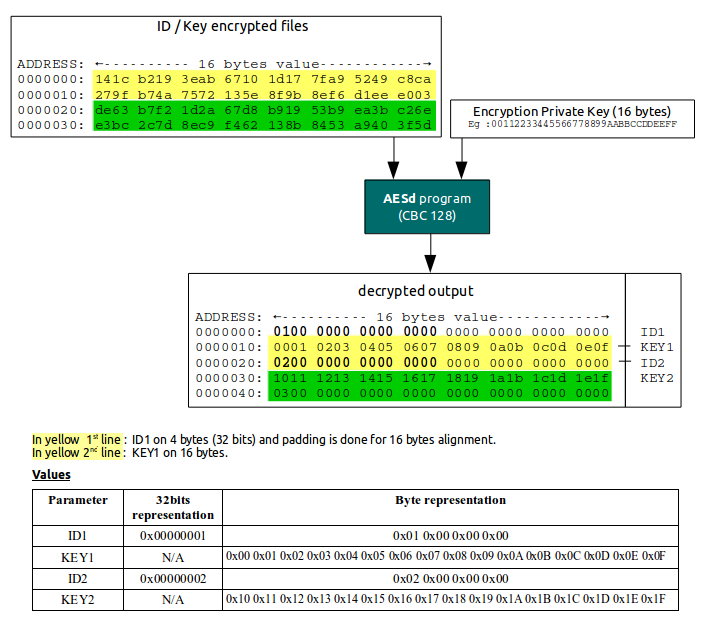
The encrypted file has the following format : ADDRESS followed by 16 bytes value
Example
0000000: 141c b219 3eab 6710 1d17 7fa9 5249 c8ca ....>.g.....RI..
0000010: 279f b74a 7572 135e 8f9b 8ef6 d1ee e003 '..Jur.^........
0000020: de63 b7f2 1d2a 67d8 b919 53b9 ea3b c26e .c...*g...S..;.n
0000030: e3bc 2c7d 8ec9 f462 138b 8453 a940 3f5d ..,}...b...S.@?]
How to decrypt the file
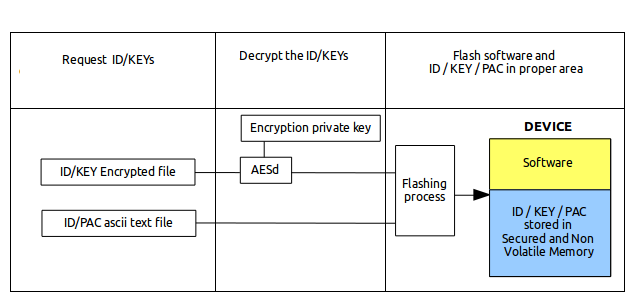
The way to decrypt the file is to use a software decryption tool based on CBC-128 along with the Encryption Private key (16 bytes).
The Encryption private key
The Encryption private key can be found in CRA web site in the Group tab. The only usage of this key is for decryption : it is unic per Manufacturer.
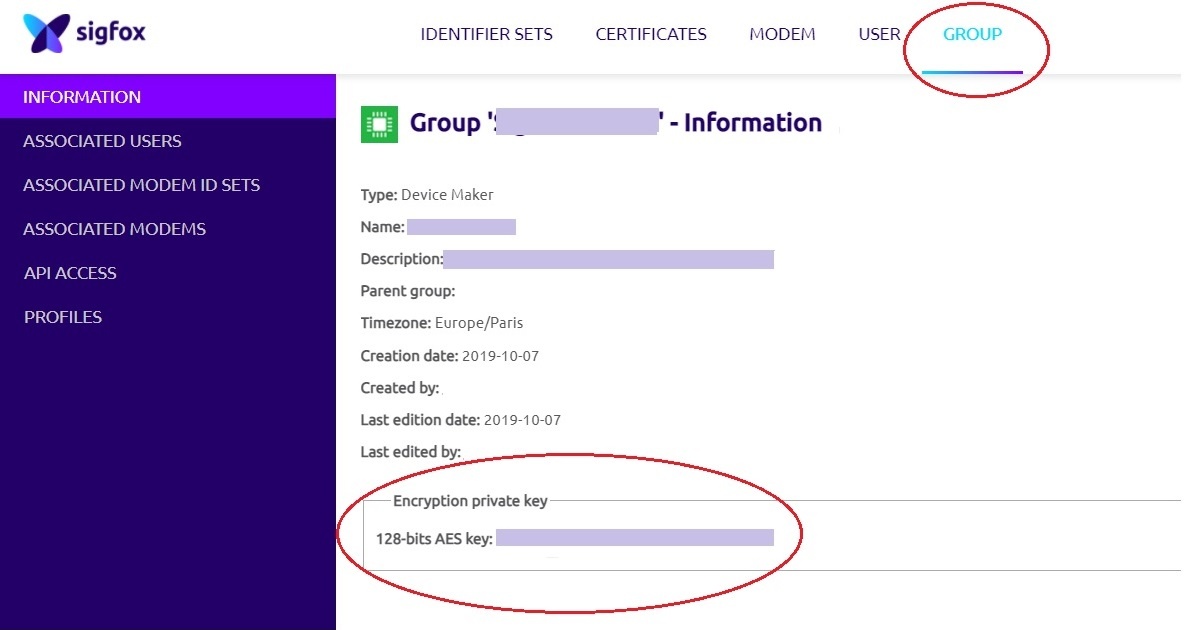
Here is a capture of the Encryption Private key in the Group tab.
The decryption software
Sigfox provides a software tool to be able to decrypt the ID / KEY encrypted file : this is names AESd : this is an example for decryption but Manufacturer can modify it to match its production flashing bench constraints.
This software is decrypting the full batch of ID/KEY but it should be better to extract one by one each ID/KEY from encrypted file to ensure no complete batch exists in clear format on the flashing bench.
AESd extracts each 16 bytes block and decrypt it with the Encryption Private Key : the output format is ADDRESS followed by 16 bytes value, containing the ID on the first line and the KEY on the next one.
ID and keys are stored alternatively on 16 bytes blocks to be decrypted on the fly by the AESd program.
This allows to decrypt only the ID/KEY couple of data without decrypting the whole file for security reasons.
Example
Build the AESd
Get the software from the CRA web site and compile it with following instructions :
gcc AES_Decrypt.cpp -o AESd ( or g++ )
Usage
./AESd <Encryption private key on 32 ascii(16bytess)> <input_encrypted_file_name> <output_decrypted_file_name>
Example
./AESd 00112233445566778899AABBCCDDEEFF id_key_encrypted.bin id_key.bin
Once you have the tool operational, you can use your CRA account and decrypt real files from CRA web site.
ID / PAC clear text ASCII files
This file contains the ID and associated initial PAC for a specific device. Once the PAC is used for registration the first PAC, its initial value is obsolete.
A new PAC is generated by the backend.
Format of the file :
ID1;INITIAL_PAC1;COMPANY
ID2;INITIAL_PAC2;COMPANY
....